Cybersecurity as a regulatory requirement of MDR and IVDR: a guide to EN IEC 81001-5-1:2022

For Medical Devices and in vitro diagnostic Medical Devices, cybersecurity is essential to satisfy the General Safety and Performance Requirements (GSPR) outlined in Annex I of the MDR (EU) 2017/745 and IVDR (EU) 2017/746 regulations.
In this context, the standard EN IEC 81001-5-1:2022 – Health software and health IT systems safety, effectiveness and security – represents the state of the art. It is the fundamental tool for translating cybersecurity requirements into structured processes throughout the entire medical device lifecycle, from design to post-market surveillance.
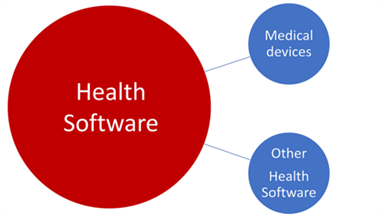
Figure 1 The scope of EN IEC 81001-5-1: a single standard for Medical Devices and other Health Software.
Scope of Application
The EN IEC 81001-5-1:2022 standard, transposing IEC 81001-5-1:2021, addresses the manufacturers’ need to define the software lifecycle processes and activities required to release cyber-secure and reliable products. The scope of this EN standard is broad, encompassing the entire Health Software ecosystem.
This technical standard is intended for software designed for:
- Managing, maintaining, or improving the health of individuals;
- The delivery of care;
- Integration into a medical device (Software in a Medical Device, SiMD) or functioning as stand-alone software (SaMD).
From a regulatory perspective, the standard is the most advanced reference for demonstrating compliance with the GSPR required by MDR and IVDR.
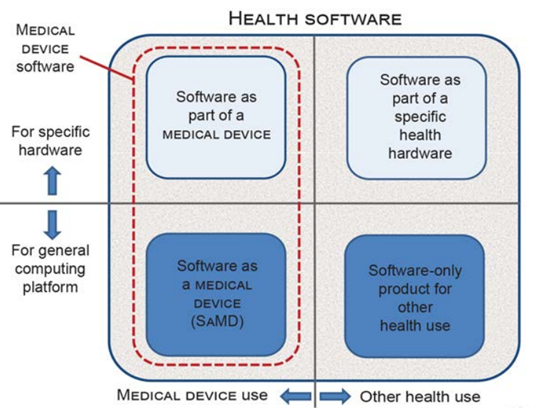
Figure 2 – Scope of the EN IEC 81001-5-1:2022 standard.
State of the Art for Cybersecurity
As of April 14, 2021, the European Commission included EN IEC 81001-5-1 in the list of technical standards slated for harmonization under the MDR and IVDR regulations.
While awaiting formal adoption, it is already universally recognized by Competent Authorities and Notified Bodies as the state of the art for health software cybersecurity. This means it represents the level of knowledge and best practices currently considered the minimum acceptable reference to demonstrate compliance with cybersecurity requirements.
Furthermore, January 20, 2025, marked the Date of Withdrawal (DOW) for conflicting national standards, as provided by MDR and IVDR. This transition has consolidated the role of EN IEC 81001-5-1 as the primary European reference for ensuring software security in the healthcare sector.
Activities and Responsibilities in the Lifecycle
The regulatory clauses of EN IEC 81001-5-1 specify activities under the direct responsibility of the manufacturer that must be performed throughout the software lifecycle.
Key activities include:
- Cybersecurity planning from the earliest design stages;
- Vulnerability assessment and mitigation;
- Implementation of technical and organizational controls;
- Secure software updates;
- Verification and validation of security functions;
- Post-market cybersecurity risk management;
- Documentation of secure operating conditions;
- Timely communication of incidents or vulnerabilities to users.
Relationship with IEC 62304: Complementarity and Moving Beyond Classes
Although EN IEC 81001-5-1 follows the same structure as IEC 62304, it introduces significant distinct elements:
- Independence: implementing IEC 62304 is not mandatory for compliance with 81001-5-1.
- Beyond Safety Classes (A, B, C): cybersecurity activities do not follow the classification principles of IEC 62304. Since the focus is on security, protection must be transversal; a vulnerability could be exploited regardless of the device class, potentially compromising the entire health IT system.
IEC 62443 and Independence of Testing
IEC 62443 is a series of security specifications for industrial automation and control systems, partially referenced in the MDCG 2019-16 “Guidance on Cybersecurity of Medical Devices.”
- Fulfilling the requirements of EN IEC 81001-5-1:2022 supports compliance with IEC 62443-4-1.
- Security tests must be performed by parties independent of those who designed and implemented the security features themselves.
2025 Evolution: The Interpretation Sheet (ISH1)
In December 2025, the IEC released the Interpretation Sheet (ISH1:2025) to clarify specific aspects of the standard, particularly regarding software component management and risk transfer.
Key clarifications include:
- Software Items Classification: better definition of categories such as Maintained (updated by the manufacturer), Supported (managed by the operator or third parties), and Required (necessary but not directly updatable by the manufacturer).
- Risk Transfer: clarification on how operational risk transfers to the healthcare operator post-installation, while maintaining the manufacturer’s obligation to ensure information transfer through clear and comprehensive accompanying documentation.
Conclusion
The adoption of EN IEC 81001-5-1:2022, integrated with the ISH1:2025 clarifications, allows manufacturers to place Medical Devices on the market that are not only clinically effective but also cyber-secure. With the definitive withdrawal of conflicting national standards, this standard stands as the pillar for health software compliance.
SOURCES:


